Secure and Modernize Your MUMPS Applications
Automated security scanning, compliance-ready SAST reports, and editor intelligence for the teams that keep healthcare, finance, and government systems running. First-class YottaDB & GT.M support.
Advanced Tooling for MUMPS/M
Reduce risk, accelerate delivery, and bring modern DevSecOps practices to your MUMPS/M codebase — without disrupting production.
mHawk
- Automated SAST — 4 taint analysis rules + 32 diagnostic rules catch vulnerabilities before production
- Compliance-ready output — SARIF v2.1.0 for GitLab Security Dashboard, GitHub, SonarQube
- Interactive call graph reports — visualize cross-routine dependencies and taint flows
- Editor intelligence — Go to Definition, Find References, Completion in VS Code & NeoVim
- AI-assisted development — MCP server for Claude Code integration
- Compiled .o analysis — extract and scan routines from YottaDB object files
- Zero dependencies — single static binary, instant startup, minimal resource usage
mSpark
- Production HTTP server with zero-downtime reload support
- Built-in security — JWT authentication, middleware guards, modern cryptography
- Data interchange — JSON, XML, YAML serialization and validation out of the box
- Quality assurance — unit test framework, code coverage reports, Cucumber/Gherkin support
- Flexible configuration — 5-level resolution for multi-environment deployments
- Data platform — Entity Schema DSL, SQL query engine, PostgreSQL wire protocol
- API tooling — OpenAPI generator, well integrated with Entity Schema definitions
- No external runtime — runs anywhere YottaDB runs
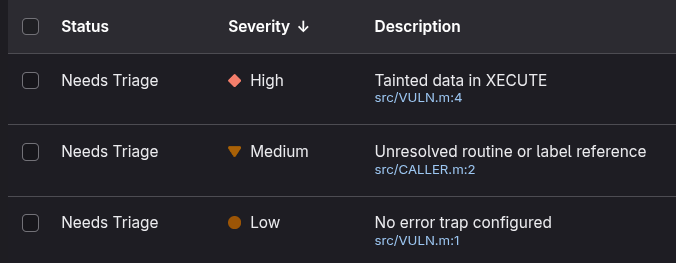
Find Vulnerabilities Before They Reach Production
mHawk provides the first purpose-built SAST engine for MUMPS/M. Identify injection risks, taint flows, and coding errors across your entire codebase — automatically.
- Taint analysis — traces untrusted input from READ/HTTP through to indirection, XECUTE, OPEN, and global dispatch sinks
- 32 diagnostic rules — duplicate labels, unresolved references, routine name mismatches, unreachable code
- SARIF v2.1.0 output — industry-standard format for audit trails and compliance reporting
- Deterministic results — identical input always produces byte-identical output across runs
- Interactive call graphs — HTML reports showing cross-routine dependencies and taint propagation paths
- Configurable rules — YAML config for custom taint sources, sanitizers, sensitive routines
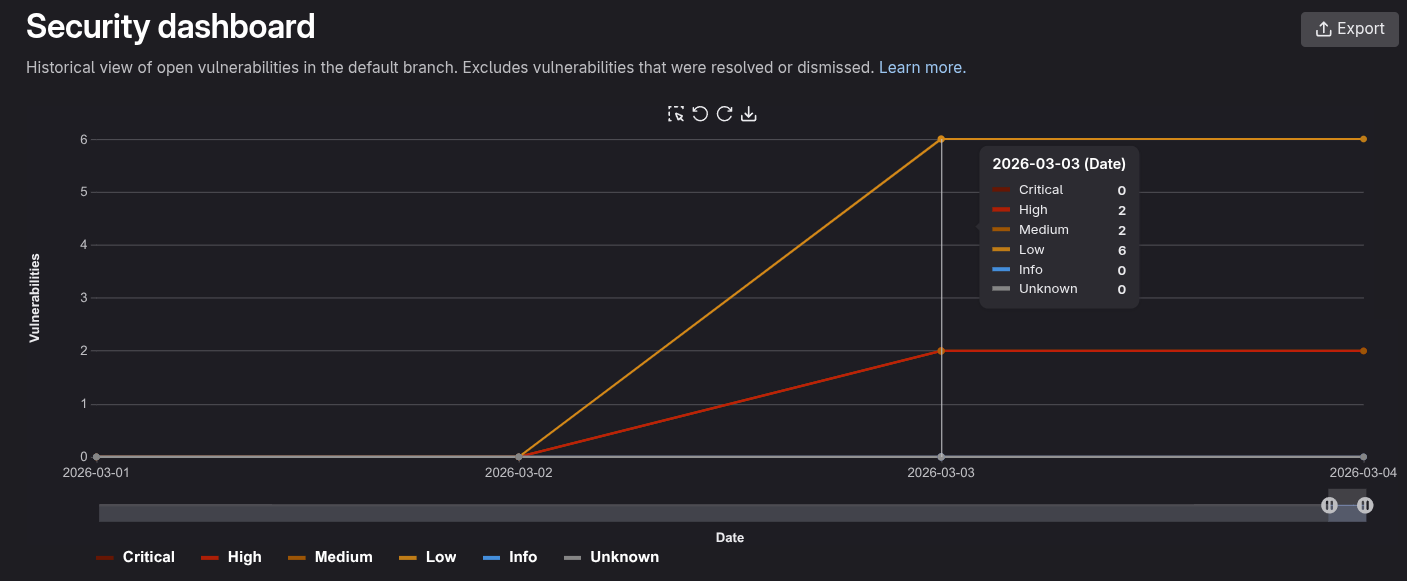
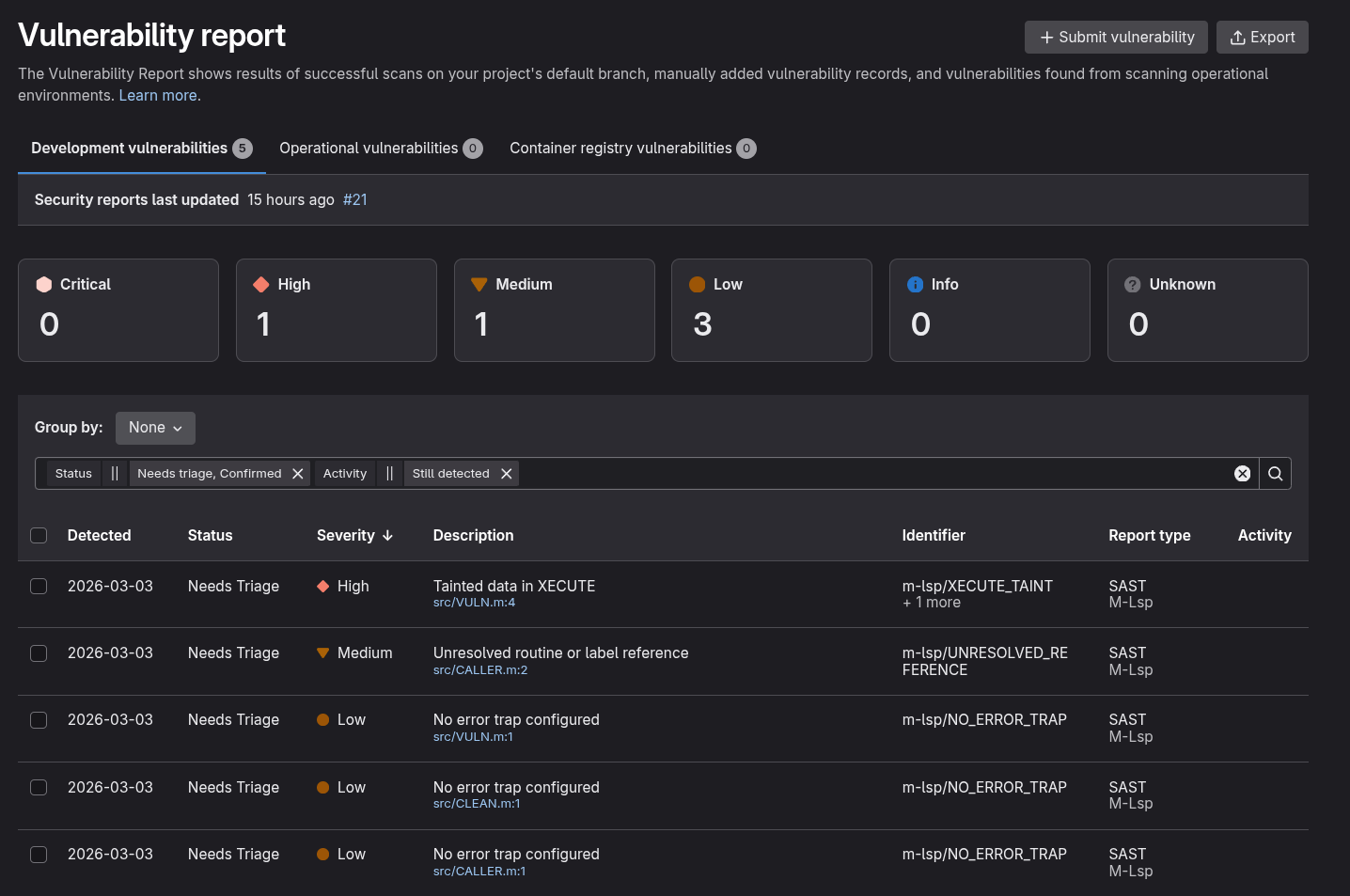
Drop Into Your Existing Pipeline
Add MUMPS security scanning to your CI/CD in minutes. Native integration with GitLab Security Dashboard, GitHub Advanced Security, and SonarQube.
- Native GitLab SAST JSON output — appears in Security Dashboard
- Seamless CI pipeline integration via .gitlab-ci.yml
- Merge request security widget shows new findings inline
- GitLab Pages for interactive call graph HTML reports
- SARIF v2.1.0 for GitHub Security Dashboards & SonarQube
- Deterministic output — identical input always produces identical results
Platform Support
Run on your existing infrastructure — no lock-in.
YottaDB
Full dialect support including local labels, object file analysis
GT.M
Compatible with GT.M routine conventions and globals
Caché / IRIS
InterSystems dialect profile — classes, macros, $SYSTEM (mHawk only)
Nix / NixOS
First-class Nix flake — reproducible builds and environments
Docker / Podman
Container images for CI and development
Single Binary
Static Rust binary — no runtime dependencies, instant startup
Ready to Secure Your M Codebase?
Whether you need security scanning for compliance, tooling for a legacy codebase, or are building new with YottaDB, we can help.
IDEA Systems
Enterprise IT consulting with 30+ years of experience. Developer tools and consulting for organizations running MUMPS/M in production.
Contact UsReference Material
- GT.M / YottaDB Documentation →Programmer's guide, administration, and reference
- YottaDB →Official YottaDB project site
- YottaDB Documentation →Multi-Language Programmer's Guide, Admin Guide
- YottaDB Source (GitLab) →Source code, issues, and contributions

